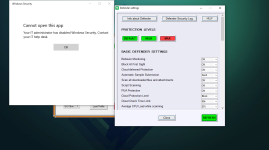
One question about the Firewall Hardening tool. The Firewall "H_C Recommended settings" are not applied automatically upon installation of H_C when you click "Apply recommended settings" right? I will need to apply them manually in the Firewall Hardening module?
I ask that because the rules windows at the moment is empty on my PC.
I ask that because the rules windows at the moment is empty on my PC.