Andy, I am getting a few of these lately
Any idea what might be trying to use Wmic?
Is it possibly connected to Office 365?
Because Office stopped working this morning, I am in the middle of an online repair of it right now.
Maybe it uses Wmic to validate itself, or something?
It is Office 365 ProPlus.
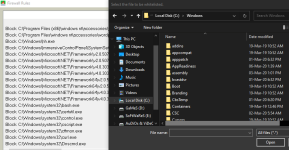
Code:
Access to C:\WINDOWS\System32\Wbem\wmic.exe has been restricted by your Administrator by location with policy rule {1016bbe0-a716-428b-822e-5e544b6a3155} placed on path Wmic.exe.Is it possibly connected to Office 365?
Because Office stopped working this morning, I am in the middle of an online repair of it right now.
Maybe it uses Wmic to validate itself, or something?
It is Office 365 ProPlus.