Did this issue persist after a reboot (adding CFA exclusions may require a reboot)?@Andy Ful
Came across something interesting when I was converting a word document to PDF and later deleting the PDF.
- Trying to convert an existing word document to PDF using Microsoft Word 2013 would not go through.
- The word document was under a protected folder and the PDF was going to be saved under the same directory.
- Protection history lists WINWORD.EXE as the app/process.
- I allowed the process via Protection history.
- An entry in ConfigureDefender CFA exclusions is now listed:
C:\Program Files\Microsoft Office 15\root\office15\WINWORD.EXE- Later when trying to delete the PDF document, the deletion was blocked.
- Protection history lists explorer.exe as the app/process.
- I allowed the process via Protection history.
- An entry in ConfigureDefender CFA exclusions list is now listed:
C:\Windows\explorer.exe
My questions are:
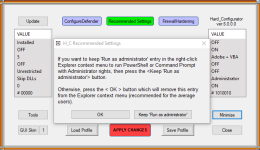
I have attached my current configuration to this post for reference. I think the only modifications I made compared to my 5.0.0.0 configuration was:
- What caused CFA to trigger these blocks in H_C 5.1.1.1/.2?
- I did the same actions as above on Friday and they weren't blocked. I can't remember if this was before or after I updated to version 5.1.1.1/.2.
- Do the explorer.exe and winword.exe CFA exclusions pose a security risk?
- Enabled Harden Archivers
- Enabled Harden Email Clients
- Enabled Allow MSI (which turns Update Mode to OFF)
Can you delete files in that protected folder directly from the Explorer?
Please, look at the H_C Log (<Tools><Blocked Events / Security Logs>) if any process was blocked at the time of file conversion.
Deleting anything in CFA protected folders from the Explorer should not be related to any H_C setting profile (also yours). But anyway, other processes can be involved, when the deletion is made by MS Office applications. You can check it by loading All_OFF.hdc profile - it will remove all H_C settings, except ConfigureDefender and FirewallHardening.