Most students usually do this.How does a teacher handle the student who neglects to read or study?
Hard_Configurator - Windows Hardening Configurator
- Thread starter Andy Ful
- Start date
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
I have just finished a quick test of Smart App Control on Windows 11 (Insider). It is much more useful than I thought.
After downloading 30 fresh applications from Softpedia it gave slightly fewer false positives compared to Norton 360, Windows SmartScreen, or Defender ASR prevalence rule.
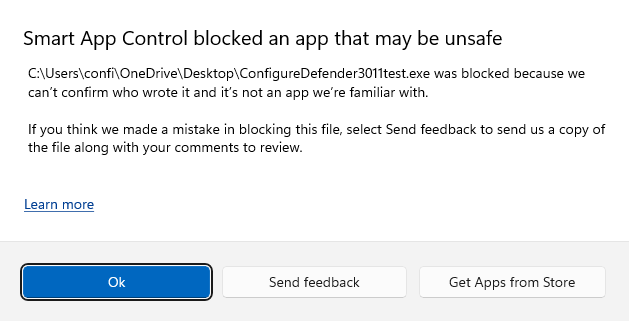
I compiled a fresh & unsigned version of ConfigureDefender to see what will happen:
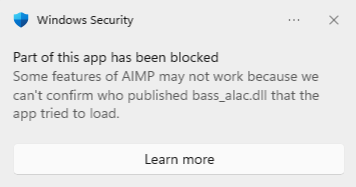
In my test, the digitally signed applications were installed & run without issues (except for two events). A few installations were blocked (some were partially blocked).:
The cons (for some people) can be that the blocked installer or application cannot be allowed/whitelisted/excluded by the user. It can be only submitted to Microsoft as a false positive in the Smart App Control category. For now, Smart App Control cannot be temporarily turned off.
It would be interesting to test Defender + Smart App Control in Malware Hub.
After downloading 30 fresh applications from Softpedia it gave slightly fewer false positives compared to Norton 360, Windows SmartScreen, or Defender ASR prevalence rule.
I compiled a fresh & unsigned version of ConfigureDefender to see what will happen:
In my test, the digitally signed applications were installed & run without issues (except for two events). A few installations were blocked (some were partially blocked).:
The cons (for some people) can be that the blocked installer or application cannot be allowed/whitelisted/excluded by the user. It can be only submitted to Microsoft as a false positive in the Smart App Control category. For now, Smart App Control cannot be temporarily turned off.
It would be interesting to test Defender + Smart App Control in Malware Hub.
Last edited:
It has never been for Windows 10 only. As you can see in the help files it is for Windows Vista, 7, and 8+.H_C is for Win 10 only ?
because I'm on Win 11
Please read the "What_is_new.txt" (it is displayed after installing H_C) for changelog details.
There is no difference in how the H_C works on Windows 10 and 11.
Last edited:
Ok it is an another french NAS forum which someone said me that...It has never been for Windows 10 only. As you can see in the help files it is for Windows Vista, 7, and 8+.
Please read the "What_is_new.txt" (it is displayed after installing H_C) for changelog details.
There is no difference in how the H_C works on Windows 10 and 11.
Thanks !
Why ask on forums? Are the H_C website info, H_C help files and manual as bad?Ok it is an another french NAS forum which someone said me that...
Thanks !
Edit.
I know that many people do not read easily the manuals in English, so it is easier for them to ask someone.
Last edited:
Still learning from this thread. I get easily led astray often by 3rd-party capabilities but built-in restrictions are just as if not more effectiveThe H_C thread is also an educational thread, about how to use Windows built-in security.
No, I ask on NAS forum why I don't access at my NAS. And, I have "disable SMB" on "???" H_C settings. And when I was found that, I said that, why. And someone, say me that H_C its only create for Win 10 and that the reason why I demand it there.Why ask on forums? Are the H_C website info, H_C help files and manual as bad?
View attachment 267624
Edit.
I know that many people do not read easily the manuals in English, so it is easier for them to ask someone.
Thats the reason why.
I completely forget this option, and on "???" its ON123 I guess for me.
I put on ON1 and the issue is resolve.
(sorry for my bad english)
...
I put on ON1 and the issue is resolve.
Is your NAS problem solved?
If you can see "????" setting then it is a non-standard setting that was not set by the H_C. The H_C just read it from the registry but could not recognize it as the standard one. The H_C Recommended Settings do not change the SMB settings.
You have three options in H_C related to SMB. Start from SMB123 and restart the computer if NAS works then OK. If not then use SMB1 setting. If both do not work then use the OFF setting. If NAS does not work with the OFF setting then the issue is not related to the H_C.
Anyway, you can also Switch OFF the H_C protection (it is simple), restart the computer, and see if NAS works or not. If not, then you have a problem that can be solved on NAS forums.
Last edited:
Yes it is resolve. Because I have put on ON1 and only SMB 2 and 3 are active...Is your NAS problem solved?
If you can see "????" setting then it is a non-standard setting that was not set by the H_C. The H_C just read it from the registry but could not recognize it as the standard one. The H_C Recommended Settings do not change the SMB settings.
You have three options in H_C related to SMB. Start from SMB123 and restart the computer if NAS works then OK. If not then use SMB1 setting. If both do not work then use the OFF setting. If NAS does not work with the OFF setting then the issue is not related to the H_C.
Anyway, you can also Switch OFF the H_C protection (it is simple), restart the computer, and see if NAS works or not. If not, then you have a problem that can be solved on NAS forums.
Because SMB 1.0 is bad for the ransomware risk...
All SMB protocols can be vulnerable in some way, but SMB 1.0 is the most attacked. Anyway, If your NAS uses SMB 2&3, then these protocols must be enabled.Yes it is resolve. Because I have put on ON1 and only SMB 2 and 3 are active...
Because SMB 1.0 is bad for the ransomware risk...
Do you think that that feature will require a fresh install even in the final version? I doubt that many people will take advantage of it if it requires a fresh install.I have just finished a quick test of Smart App Control on Windows 11 (Insider). It is much more useful than I thought.
After downloading 30 fresh applications from Softpedia it gave slightly fewer false positives compared to Norton 360, Windows SmartScreen, or Defender ASR prevalence rule.
I compiled a fresh & unsigned version of ConfigureDefender to see what will happen:
View attachment 267619
In my test, the digitally signed applications were installed & run without issues (except for two events). A few installations were blocked (some were partially blocked).:
View attachment 267621
The cons (for some people) can be that the blocked installer or application cannot be allowed/whitelisted/excluded by the user. It can be only submitted to Microsoft as a false positive in the Smart App Control category. For now, Smart App Control cannot be temporarily turned off.
It would be interesting to test Defender + Smart App Control in Malware Hub.
It is early-stage in Insider, so everything is possible. The current version is not practical.Do you think that that feature will require a fresh install even in the final version? I doubt that many people will take advantage of it if it requires a fresh install.
Smart App Control (SAC) is a similar idea to Forced SmartScreen (FS), already applied in the H_C. But there is an important difference. SAC can block the downloaded application installers with MOTW and also any executable (EXE, DLL, MSI, etc.) dropped to disk (no MOTW). FS can block only executables with MOTW (mostly application installers downloaded via web browser). So, SAC can be more robust when the system is already compromised (via malware or exploit).
if SAC would be more practical, then it could replace FS. But, this would require that SAC's alerts should behave similarly to the SmartScreen alerts. So, the user could choose to allow the execution, and the execution could be controlled by the system policy.
One could use the H_C Basic_Recommended_Settings + SAC (or SWH + SAC) to get similar but more usable protection as with the H_C Strict_Recommended_Settings.
Anyway, such a configuration would not be as usable as the H_C Recommended_Settings. The Forced SmartScreen allows almost all software auto-updates because they are downloaded without MOTW, so they are ignored by SmartScreen. On the contrary, the SAC blocks are independent of MOTW, so it can still block many software auto-updates, especially when the software is not digitally signed. But, this would not be a serious issue for digitally signed applications (except those with low reputation or prevalence).
Edit.
SAC can also block many fileless attacks that use DLL hijacking or standard DLL injections. So in the home environment, it could be very good protection even without H_C or SWH. Of course, some advanced techniques realized via scripts (custom DLL loaders, process hollowing, shell code injections, etc.) are not covered by SAC - but these methods are uncommon in widespread attacks.
if SAC would be more practical, then it could replace FS. But, this would require that SAC's alerts should behave similarly to the SmartScreen alerts. So, the user could choose to allow the execution, and the execution could be controlled by the system policy.
One could use the H_C Basic_Recommended_Settings + SAC (or SWH + SAC) to get similar but more usable protection as with the H_C Strict_Recommended_Settings.
Anyway, such a configuration would not be as usable as the H_C Recommended_Settings. The Forced SmartScreen allows almost all software auto-updates because they are downloaded without MOTW, so they are ignored by SmartScreen. On the contrary, the SAC blocks are independent of MOTW, so it can still block many software auto-updates, especially when the software is not digitally signed. But, this would not be a serious issue for digitally signed applications (except those with low reputation or prevalence).
Edit.
SAC can also block many fileless attacks that use DLL hijacking or standard DLL injections. So in the home environment, it could be very good protection even without H_C or SWH. Of course, some advanced techniques realized via scripts (custom DLL loaders, process hollowing, shell code injections, etc.) are not covered by SAC - but these methods are uncommon in widespread attacks.
Last edited:
In future versions you could add the option to turn on SAC to H_C, thank you very much.
The H_C settings are reversible, but SAC is not. After enabling SAC you cannot disable it. We must wait for more improvements.In future versions you could add the option to turn on SAC to H_C, thank you very much.
I don't think this is correct, you can disable SAC but can't re-enable again without reset/reinstall Windows.The H_C settings are reversible, but SAC is not. After enabling SAC you cannot disable it. We must wait for more improvements.
The choices, "ON" and "OFF" are irreversible. It means that you must reset/reinstall Windows to change the setting.I don't think this is correct, you can disable SAC but can't re-enable again without reset/reinstall Windows.
@Andy Ful
I see in the article below:

 4sysops.com
4sysops.com
it mentions to include psm1 as a designated file type when using SRP to enforce PowerShell CLM, but in the H_C file types I don't see that one:
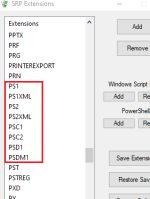
If I try adding more PowerShell script file types, psm1 is not offered. I'm sure there's a perfectly valid reason for this, but I'm just curious as to why it isn't included.
I see in the article below:

Mitigating PowerShell risks with Constrained Language mode – 4sysops
PowerShell is a robust tool that can control almost all components of Windows and applications such as Exchange. It can therefore cause great damage in the hand
it mentions to include psm1 as a designated file type when using SRP to enforce PowerShell CLM, but in the H_C file types I don't see that one:
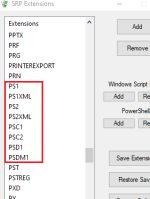
If I try adding more PowerShell script file types, psm1 is not offered. I'm sure there's a perfectly valid reason for this, but I'm just curious as to why it isn't included.
@Andy Ful
I see in the article below:
https://4sysops.com/archives/mitigating-powershell-risks-with-constrained-language-mode/
it mentions to include psm1 as a designated file type when using SRP to enforce PowerShell CLM, but in the H_C file types I don't see that one:
The list was created several years ago. Now, adding other PowerShell extensions except PS1 is not necessary on Windows Home and Pro:
- The user cannot accidentally run any PowerShell file. Windows built-in default settings will force opening it in the notepad or the file will not be opened at all (extension not registered).
- The PSM1 files do not support the "Run with PowerShell" option in the right-click Explorer context menu.
Finally, Hard_Configurator blocks by default all possible PowerShell scripts (also PSM1) not by SRP, but via the <Block PowerShell Scripts> option from the H_C right panel.
I could add the PSM1 extension, but I did not test it, so I do not know how this could impact the users who skipped the <Block PowerShell Scripts> option. The PSM1 files are for PS1 files like DLLs for EXE files. The PSM1 modules are used to store functions that can be imported by PS1 scripts.
Last edited:
You may also like...
-
-
FAI Tells It Like It Is - Microsoft's Wonky Default Deny Roadmaps, Users as Guinea Pigs, "Dilemmas and Paradoxes," and Why SRP Remains King
- Started by ForgottenSeer 114717
- Replies: 44
-
Microsoft testing Windows 11 batch file security improvements
- Started by Parkinsond
- Replies: 0
-
Malware News CrySome RAT : An Advanced Persistent .NET Remote Access Trojan
- Started by Khushal
- Replies: 3
-
