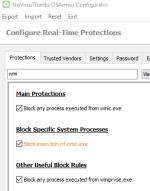
How did you understand the info in the help file for <MS Office> option?Let me get this right. That is, if I want to use desktop Office, do I need to set the Current user restriction of MS Office to ON2, or ON1? Will it be possible to open .xls, .xlsx files with this setting?
Edit.
This help requires a correction - these restrictions works also on MS Office 2019.
Last edited: